Australia Begins Mass Data Retention
Large amounts of telecommunications metadata must now be kept for, at least, two years by Australian telecommunications companies after a new law that came into effect recently.
It includes data on who called or texted whom and for how long, as well as location, volume of data exchanged, device information and email IP data. Some data was already being retained but the new rules expand on this. It also makes it much easier for authorities to access the records.
The new law has caused heated debate among Australians with some justifying the expanded data retention and others pointing out flaws in the plan.
The bill was introduced to the Australian parliament when current prime minister, Malcolm Turnbull, was communications minister. He called it "critical" for security agencies and law enforcement, citing investigations into domestic terrorism.
"No responsible government can sit by while those who protect us lose access to vital information, particularly in the current high threat environment," he said at the time, in a joint statement with Attorney-General George Brandis.
The government has stressed that the data retained is only "metadata" and does not include the content of calls and messages themselves. The law also does not require firms hold on to a web users' browsing history. The authorities also point out that some of this data was already being retained by telecommunications companies, albeit on an ad hoc basis.
Third-party email, video, and social media platforms such as Gmail, Hotmail, Facebook and Skype are also exempt from some of the data retention requirements, as are internal email and telephone networks, such as those provided by corporate firms and universities.
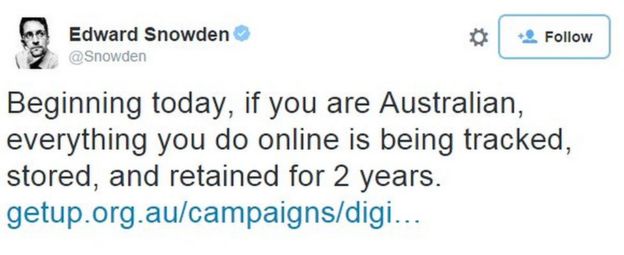
NSA leaker Edward Snowden weighed in on the new rules
Opponents point out that, considered in entirety, such metadata paints a detailed picture of what people are doing, even if the content of messages is not included. They also point out that while terrorism and child abuse investigations are often cited, the new rules allow for data to be requested for much more minor crimes. The process of request has also become much easier. Typically it will not now require a warrant. It will still take a warrant to access a journalist's data to identify their sources, but that hearing will take place in private. And no warrant is needed for government agencies to search the data of its own ranks if that is where they suspect the source lies.
There are fears too that having introduced the legislation, it will be tightened further in future. The multi-million dollar scheme has also come under fire for its cost, which will be partially borne by the government.
Australian Green Party Senator Scott Ludlam tweeted that it was "absurdly expensive and complex for ISPs to implement, trivially easy for anyone to defeat" - a reference to the prime minister's admission that he also uses encrypted messaging apps.
The Green Party voted against the bill, along with six independent senators, but was overwhelmingly defeated.
The security of the servers used to hold the data has also been a question, with mass data breaches becoming increasingly common around the world.
There have also been reports that some companies are unsure whether they are covered by the new laws and exactly what data they need to keep.
BBC:http://http://bbc.in/1QmW9pt


























