Countdown: 10 Things Cyber Crooks Could Do To Your Computer, Without Even Touching It
Protect Your Computer With Security Software
Most computer viruses can be blocked simply by downloading, and updating, security software. You may not have symptoms, but you may still be infected. Check these out…
10. Have fun with your computer
If your CD tray has ever opened on its own or your mouse has suddenly become erratic this could be a sign of an infection. Some viruses allow criminals to ‘play about’ with your device including switching off your monitor and turning your text to speech. Download and update your security software.
9. Use your computer to force other websites to close down
Criminals can use your computer to attack other websites in what is described as a Distributed Denial of Service (DDoS), whereby websites are overloaded with unnecessary internet traffic. DDoS attacks can bring down small business or important public information websites. Download and update your security software.
8. Spreading infections
Cyber criminals want to get their viruses into as many devices as possible, and they don’t just use websites and emails to do it. Infected CDs and USB sticks, and your WiFi network, are among the other ways they spread malicious software. Download and update your security software.
7. Force your computer to click on websites you don’t want to visit
Some viruses can control which websites you visit; even if you think you’ve typed in a legitimate site it could redirect you to inappropriate material or more malicious software, which infects your device further. Download and update your security software.
6. Randomly chat to you
If you’re infected you could find yourself speaking directly to a criminal. Through a virus, cyber crooks can talk directly to you with a pop-up chat window. And via this chat, criminals may send you infected web links or even blackmail you into doing what they say. Download and update your security software.
5. Take control of your computer
Some viruses allow criminals to take control of your computer without even touching it. This allows them to open files, folders and emails, and take pictures of what appears on your screen. Download and update your security software.
4. Hijack your personal files and make you pay to get them back
By using viruses crooks can access your personal documents, music and photos, and then hijack them by demanding ransoms from you to get access to them again. If you don’t pay they threaten to delete them forever. Download and update your security software.
3. Record every key you hit on your keyboard
Viruses allow crooks to record every button you strike on your keyboard, either live as you type it or stored on their hard drive to be used later to access your personal information and banking details. Download and update your security software.
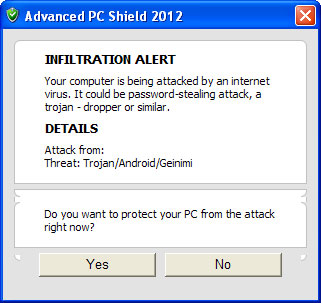
2. Steal your passwords
It’s always worth creating complex passwords, but if you’re not protected then you risk cyber crooks using viruses to collect your usernames and passwords. Download and update your security software.
1. Hack your webcam
Some viruses allow criminals to remotely access your webcam and microphone, and in some cases they may take screen shots from your cam to later blackmail you. Download and update your security software.
Next steps:
Download security software to keep your devices secure. If you already have security software installed, make sure it’s kept up to date. Find out more https://www.cyberstreetwise.com/security-software
Buzzfeed:http://http://bzfd.it/1uDtWPT


























