US Defense Secretary Defines New Cybersecurity Strategy
Uploaded on 2015-05-04 in NEWS-Cybersecurity News, INTELLIGENCE--USA, GOVERNMENT-National, FREE TO VIEW
While the security industry gathered in San Francisco for the massive RSA Conference, just down the road at Stanford University in Palo Alto, Defense Secretary Ash Carter described in a speech there the Department of Defense's updated cybersecurity strategy that includes more transparency about its mission and operations and a "renewed partnership" with the technology industry.
"As Secretary of Defense, I believe that we in the Pentagon – to stay ahead – need to change and to change we need to be open, as I say, we have to think outside of our five-sided box," Carter said in a speech at Stanford yesterday.
At the heart of the DoD's cyber defense strategy is deterrence, stopping malicious behavior before it occurs, and identifying from where the attack came. "In some ways, what we’re doing about this threat is similar to what we do about more conventional threats. We like to deter malicious action before it happens, and we like to be able to defend against incoming attacks – as well as pinpoint where an attack came from," he said. "We’ve gotten better at that because of strong partnerships across the government, and because of private-sector security researchers like FireEye, Crowdstrike, HP – when they out a group of malicious cyber attackers, we take notice and share that information."
But the deterrence strategy doesn't mean DoD won't take other actions when needed, he said. "And when we do take action – defensive or otherwise, conventionally or in cyberspace – we operate under rules of engagement that comply with international and domestic law."
"We must continue to respect, and protect, the freedoms of expression, association, and privacy that reflect who we are as a nation. To do this right, we again have to work together. And as a military, we have to embrace openness," Carter said. "Today dozens of militaries are developing cyber forces, and because stability depends on avoiding miscalculation that could lead to escalation, militaries must talk to each other and understand each other’s abilities. And DoD must do its part to shed more light on cyber capabilities that have previously been developed in the shadows."
Carter shared a story about an attack earlier this year on DoD's unclassified military networks by Russian hackers. "It's never been publicly reported," he said of the incident.
"Earlier this year, the sensors that guard DoD’s unclassified networks detected Russian hackers accessing one of our networks. They’d discovered an old vulnerability in one of our legacy networks that hadn’t been patched," he noted.
The department detected the compromise and a team of incident responders was on the case within 24 hours, he said. "After learning valuable information about their tactics, we analyzed their network activity, associated it with Russia, and then quickly kicked them off the network, in a way that minimized their chances of returning."
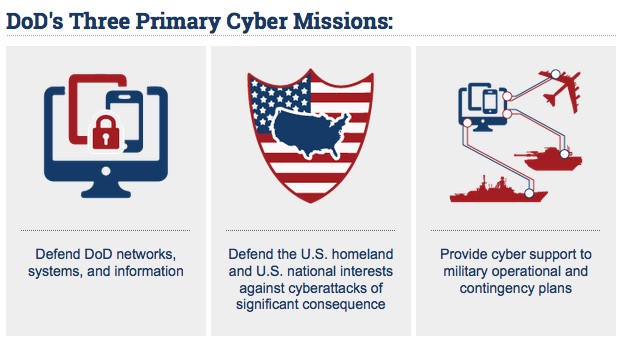
Carter said the department also has a goal to better defend DoD information networks, lock down data, and protect military missions from cyberattack. "We do this in part through deterrence by denial, in line with today’s best-in-class cybersecurity practices – building a single security architecture that’s both more easily defendable, and able to adapt and evolve to mitigate both current and future cyber threats. This to replace the hundreds of networks – separate networks – that we now operate in the Department of Defense," he said.
"We have to strengthen our network defense command and control to synchronize across thousands of these disparate networks, and conduct exercises in resiliency…so that if a cyberattack degrades our usual capabilities, we can still mobilize, deploy, and operate our forces in other domains – air, land, and sea – despite the attack," he said.
Carter this week ordered the consolidation of IT services in DoD and in the Washington, DC capital region, he said, for better defenses and cost savings.
Carter said DoD will work more closely with the FBI, DHS, and other law enforcement to strengthen its cyber operations. "There are clear lines of authority in our government about who can work where, so as adversaries jump from foreign to U.S. networks, we need our coordination with our government to operate seamlessly."
Dark Reading: http://ubm.io/1zyiMUj


























