Paying for Non-Secrets
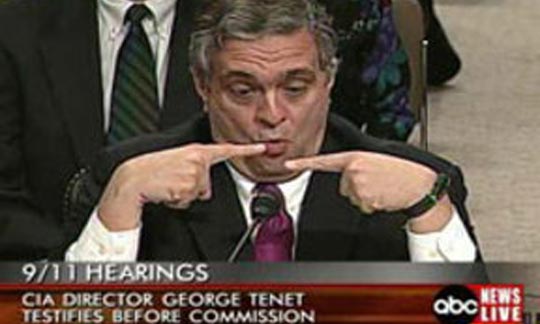
Former Director of Central Intelligence George Tenet famously said when asked about so-called open source (unclassified) intelligence, “we only pay for secrets.” He spoke with the confidence of a man born and raised in the world of the 20th century spy and the Cold War.
With the massive leak of government employee information from the Office of Personnel Management (OPM), Director Tenet’s statement has been proven quite wrong for the 21st century. China and others are willing to pay for “non-secrets” and they matter.
As data breaches go, the OPM break in was not the biggest one experienced in the past few years. Target, JP Morgan Chase and a few others were larger in breath and scope. But, they did not contain information that could be used to target and engage in spying on the US government.
As an old spy, I wanted information. I wanted people’s background: where they live and had lived, who their relatives were, and what personal problems they might have. That way I could figure out how to develop a successful “relationship” with someone who would spy for me. And, also, target more successfully – not waste time on someone who did not matter. You see, the real trick is human intelligence is finding people with access to important people and their information. I don’t want to recruit the Secretary of State -- too big, too awkward to meet and not likely to be recruited. No, I want someone on his staff or someone who has access to his staff and especially their work product.
The OPM leak contains millions of personnel files that will help China do just that. Files on government employees and their contractors with a summary of their backgrounds and what programs they have access to is quite sufficient for my targeting purposes.
In the 21st century, information contained in files like OPM need to be treated like the old fashioned state secrets were. I am sure whatever investigation there is will turn up either woefully inadequate IT security, inside actions, or both.
Welcome to 21st Century cyber conflict. Information is a weapon to use and target and cyber space is the battlefield. So far, if OPM is the indicator, the US government is getting skunked.
Ronald Marks President and Senior Partner, Intelligence Enterprises, LLC
LinkedIn: http://linkd.in/1RcRTYK


























